ITAR and CUI in Manufacturing: The Gap Between Policy and Practice
ISO 27001By Trenton Steadman
Quick Answer
What do ITAR and CUI require for manufacturers?
ITAR (International Traffic in Arms Regulations) governs export of defense-related technical data; CUI (Controlled Unclassified Information) covers sensitive government information that requires safeguarding, with handling requirements defined in NIST SP 800-171. Manufacturers handling either need clear separation between controlled and general data: an encrypted vault with multi-factor access for ITAR drawings and CUI documents, audit trails for who accessed what, and training so controlled data doesn't end up on the general network.

In a good chunk of the manufacturing companies I work with, somewhere between the front office and the production floor, there's a disconnect in how controlled information gets handled. Everyone knows ITAR data is sensitive. Everyone knows there are rules. But when I sit down with an IT Manager and a Quality Manager in the same room and ask them to walk me through what actually happens when they receive a controlled drawing, I usually get two different answers.
That gap - between what the policy says and what actually happens - is where most manufacturers are exposed. Not because they don't care, but because ITAR and CUI requirements evolved faster than their processes did.
What ITAR and CUI Actually Mean for a Manufacturer
If you're a manufacturer with aerospace or defense contracts, you're likely already dealing with these requirements in some form. ITAR - the International Traffic in Arms Regulations - governs the export of defense-related articles, services, and technical data. CUI - Controlled Unclassified Information - is a broader category covering sensitive government information that requires safeguarding but isn't classified. The handling requirements for CUI are defined in NIST SP 800-171, which has become the baseline that most defense contractors are measured against.
For a manufacturer, ITAR data might include technical drawings, process parameters for defense-related components, test data, and customer specifications. CUI can extend even further into contractual requirements, quality data, and supplier information tied to government programs.
The practical reality is that these aren't abstract compliance categories. They translate into specific questions: Where is this data stored? Who can access it? What happens when someone emails a drawing instead of using the secure system? And critically - if you're part of a multinational corporate group, how do you keep controlled information away from non-US persons who may have network access?
The Encrypted Vault Approach
One approach I've seen work well in practice is an encrypted vault system. A manufacturing client I worked with uses a dedicated software solution designed specifically for controlled data - essentially an encrypted document repository separate from the general network. Every document stored inside is encrypted at rest, and access requires multi-factor authentication through a mobile application.
The concept is straightforward: ITAR-sensitive documents and CUI go into the vault. Everything else lives on the regular network. Clean separation.
In practice, it's messier than that. When I asked the IT Manager how well people actually keep controlled data in the vault, the honest answer was that it's training-dependent. There's no automated scanning tool that catches when someone saves an ITAR drawing to a regular network share instead of the encrypted vault. They'd looked at automated classification tools - solutions that scan network traffic and flag documents containing PII or ITAR-related content - but hadn't found one that worked reliably enough to depend on.
That's a common finding. The technology for secure storage exists and works. The gap is almost always behavioral - getting every Engineer, every Sales Rep, every Program Manager to consistently use the secure channel instead of defaulting to email or shared drives because it's faster.
The CMMC Question
Manufacturers handling CUI are likely aware of CMMC - the Cybersecurity Maturity Model Certification. The question I get from most clients is whether they need external certification or if self-assessment is sufficient.
The answer depends on your contract flow-down requirements. One manufacturer I consulted with had been doing self-assessments for several years and hadn't been required to pursue external CMMC certification. But their aerospace customers were increasingly including cybersecurity questionnaires in their supplier qualification processes - essentially CMMC-aligned requirements flowing down through the supply chain even without formal certification mandates.
If you're pursuing ISO 27001, you're building a significant portion of the foundation that CMMC requires anyway. The controls around access management, incident response, risk assessment, and configuration management overlap considerably. The thinking we applied was practical: build the ISO 27001 ISMS to genuinely address your risks, and you'll be well positioned if CMMC external certification becomes a contractual requirement. Don't build two parallel systems.
Where Quality and IT Collide
In most manufacturing companies, ITAR handling lives in a gray zone between the quality department and IT. Quality owns the contract review process - they're the ones who identify when incoming work involves controlled information and flag it during order intake. IT owns the technical controls - the vault, the access permissions, the network segmentation.
Where it gets interesting is the handoff. I sat in a session where the Quality Manager pulled up their existing SOP for contract review and showed me where ITAR was referenced. The procedure was embedded within the broader contract review process - coded into the workflow rather than existing as a standalone document. Meanwhile, the IT Manager had a separate data classification policy that referenced ITAR under the "strictly confidential" tier.
Neither was wrong. But when we looked at whether anyone had mapped the complete end-to-end flow - from a sales rep receiving a request for quote on a controlled part, through contract review, to secure data handling, to production, to shipping - the pieces existed in different documents owned by different departments without a clear thread connecting them.
For manufacturers working toward ISO 27001, this is actually an opportunity. The standard requires you to identify information assets, classify them, and define handling procedures. Building that asset inventory and those handling procedures gives you a chance to connect the dots that quality and IT have been maintaining separately.
The Non-US Person Challenge
Here's where it gets uniquely complicated for manufacturers owned by foreign parent companies. ITAR restricts access to controlled technical data by non-US persons. If your parent company is based overseas and your IT infrastructure shares any resources - Active Directory, file servers, VPN access - you need clear technical and procedural controls to prevent inadvertent disclosure.
One manufacturer I worked with handled this primarily through the encrypted vault. Corporate IT personnel from the parent company could access the general network, but the vault required separate credentials that were only issued to US persons with a legitimate need to access controlled data. The quality department maintained a classified parts list, and one person was responsible for ensuring that any new part flagged as ITAR-controlled was properly routed into the secure environment.
The control works, but it depends heavily on one person doing their job consistently. When I asked about monitoring or compliance checking - some kind of periodic review to verify that controlled data hadn't leaked outside the vault - the honest answer was that it's manual and imperfect. That's not unusual, but it's worth acknowledging when you're documenting your ISMS. An auditor will appreciate a realistic description of your controls and their limitations more than a policy that claims everything is perfectly contained.
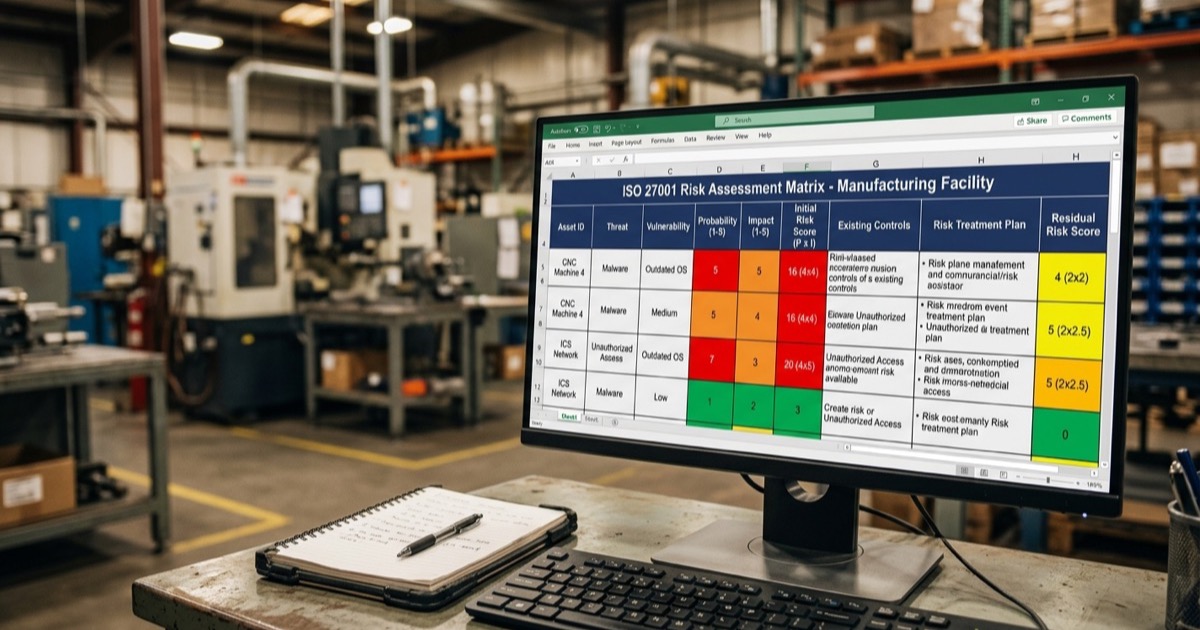
Data Classification as the Foundation
Before you can protect controlled information effectively, you need to know what you have and how sensitive it is. Data classification sounds straightforward, but in a manufacturing environment it gets complicated fast.
A typical approach uses three or four tiers - something like Public, Internal, Confidential, and Strictly Confidential - with ITAR and CUI falling into the top tier. The classification drives the handling requirements: how it's stored, who can access it, how it's transmitted, and how it's disposed of.
Where manufacturers struggle is that the classification often exists as a policy document that nobody references in their daily work. The engineer who receives a technical drawing knows intuitively that it's controlled - because the customer said so, or because it has an ITAR notice on it. But they're not checking the data classification matrix before deciding how to handle it. They're doing what they've always done, which may or may not align with what the policy prescribes.
The practical fix isn't more complex classification schemes. It's making the classification visible and actionable at the point where decisions happen. That might mean embedding ITAR flags in your ERP system so they're visible on the work order. It might mean a mandatory field in your contract review form that forces a classification decision before the order progresses. It's about building the control into the workflow, not layering policy documents on top of existing habits.
Practical Steps for Getting Your Arms Around It
- Map the actual flow, not the assumed flow. Sit down with quality, IT, engineering, and sales. Walk a controlled part from quote to shipment and document every point where controlled information is created, stored, transmitted, or accessed. You'll find gaps you didn't know existed.
- Audit vault compliance. If you're using an encrypted vault or similar solution, do a periodic check. Is everything that should be in there actually in there? Even a manual spot-check is better than assumption.
- Connect your existing documents. You probably already have ITAR references in contract review, data classification policies in IT, and handling procedures scattered across departments. Before writing new procedures, connect what exists into a coherent end-to-end flow.
- Address the non-US person question explicitly. If you have a foreign parent company, joint ventures, or multinational staff, document your technical and procedural controls for preventing inadvertent disclosure. Auditors and customers will ask.
- Build classification into workflows, not binders. The data classification policy nobody reads is less effective than an ITAR flag field on the order entry screen that forces a decision every time.
- Align with ISO 27001 if you're headed that direction. The controls you need for ITAR and CUI map directly to ISO 27001 Annex A controls around information classification, access management, and secure handling. Building them together saves effort and creates a system that actually holds together.
It's Not About Perfection
No manufacturer I've worked with has a perfect ITAR and CUI handling process. The automated scanning tools aren't reliable enough. The behavioral controls depend on people consistently choosing the secure option over the convenient one. The classification systems are only as good as the training and the workflow integration behind them.
But there's a meaningful difference between a manufacturer that understands its gaps and is working to close them, and one that has a policy on a shelf and hopes for the best. If you can show an auditor - or a customer - that you've mapped your controlled information flows, implemented reasonable technical controls, identified where the behavioral gaps are, and have a plan to address them, you're in a fundamentally stronger position than most.
If you're working through ITAR, CUI, or ISO 27001 implementation and want to talk through your approach, we offer a free initial consultation to help you figure out where you stand.
Trenton Steadman is the Lead ISO Consultant at Kaizen ISO Consulting. Since 2017 he has guided 200+ clients through ISO 9001, 14001, 45001, and 27001 certifications, with clients passing their certification audits on the first attempt. He also supports ISO 17025 and ISO 50001 engagements and holds AS9100 and IATF 16949 lead-auditor credentials. His approach is built around real operations rather than generic templates, so management systems work the day after certification, not just the day of.