ISO 27001 for Manufacturing: Beyond Tech Companies
ISO 27001By Trenton Steadman
Quick Answer
Why does manufacturing need ISO 27001?
Manufacturing organizations pursue ISO 27001 because of customer contracts (automotive, aerospace, and defense increasingly require it for Controlled Unclassified Information, ITAR data, and proprietary specifications), government contract favorability, and the operational reality that ransomware on order-entry or ERP systems can halt production without touching a single machine. Information security in manufacturing is about protecting the flow of information, purchase orders, shipping data, quality records, customer specs, that keeps production moving, not just servers and laptops.

ISO 27001 in Manufacturing: It's Not Just an IT Standard
When I bring up ISO 27001 with manufacturing clients, I get one of two reactions. Either they've never heard of it, or they assume it's something for software companies and banks. The reality is that manufacturing companies are increasingly finding themselves in the crosshairs of information security requirements - driven by customer contracts, supply chain expectations, and the uncomfortable truth that a ransomware attack can shut down a production line just as easily as it can lock up a corporate email server.
I recently worked with a steel manufacturer that was already certified to ISO 9001 and ISO 14001. They had a solid Quality Management System, good environmental controls, and a team that understood the audit process. But when their automotive and aerospace customers started requiring evidence of information security practices - and their contracts started including 24-hour incident notification clauses - they realized ISO 27001 wasn't optional anymore. It was a business requirement.
Here's what I've learned about implementing ISO 27001 in manufacturing environments, and why the standard applies differently than most online guides suggest.
Why Manufacturing Companies Are Pursuing ISO 27001
The push usually comes from one of three places: customer/corporate requirements, government contract favorability, or a close call with a security incident.
For manufacturers with automotive, aerospace, or defense clients, the conversation often starts with contracts. Controlled Unclassified Information, ITAR data, proprietary tooling specifications - these all need protection, and customers want documented evidence that you're managing it. A self-assessment might satisfy requirements for a while, but eventually someone in the supply chain asks for formal certification.
Then there's the operational reality. One Quality Manager I worked with had experienced a ransomware attack at a previous employer. The company was locked out of their EDI system entirely. Production didn't stop because the machines couldn't run - it stopped because they couldn't receive orders, ship product, or communicate with customers. The attack didn't target the production floor. It didn't need to. It just targeted the systems that the production floor depends on.
That's the piece many manufacturers miss. Information security in manufacturing isn't primarily about protecting servers and laptops. It's about protecting the flow of information that keeps production moving - purchase orders, shipping data, quality records, customer specifications, calibration data, and the ERP system that ties it all together.
What Makes Manufacturing ISO 27001 Different
Most ISO 27001 implementation guides are written for companies where the primary assets are digital - SaaS platforms, financial data, customer databases. Manufacturing environments may have some similarities but are often different, and the implementation needs to reflect that.
Your Assets Aren't Just Laptops and Servers
In a manufacturing plant, information assets include production equipment with network connectivity, industrial control systems, calibration equipment, badge access systems, and CCTV infrastructure. A steel manufacturer I worked with had assets ranging from office computers to production line controllers, custom-built calibration tracking software, and an encrypted vault system for controlled technical data. The asset inventory for their ISMS looked very different from what you'd see at a consulting firm or tech startup.
When we built out the Asset Register, we had to think about what information flows through each system and what happens if that system goes down. A calibration tracking application going offline might not sound critical, but if you can't verify that your measurement equipment is in spec, you can't ship product that requires documented quality checks.
Physical Security Is More Complex
Office-based companies worry about server rooms and maybe a front door. Manufacturing companies have multiple buildings, production floors that need to stay accessible for operations, network closets in harsh industrial environments, and sometimes multiple plant locations all within scope.
The steel manufacturer I mentioned had several plants in their scope, including an automotive and aerospace division. Each facility had its own physical security considerations - badge systems, camera coverage, secured areas for controlled information - while maintaining the operational access that production requires. You can't put the same access restrictions on a production floor that you'd put on a data center.
Your Software Isn't All Off-the-Shelf
Many manufacturers develop custom applications for processes that commercial software doesn't handle well. Calibration tracking systems, proprietary quality complaint management tools, custom purchase requisition workflows - these homegrown applications need security controls and proper development practices, but they don't fit neatly into standard IT security frameworks designed for commercial software environments.
This matters because auditors will ask about your development practices for these applications. If you've got a custom-built system managing device calibration data, they'll want to know how changes are tested, who has access to modify the code, and how you ensure data integrity. That's a very different conversation from managing patches on a commercial ERP system.
Leveraging What You Already Have
Here's the good news for manufacturers that are already certified to other ISO standards: you've done a significant amount of the foundational work. ISO 27001 shares the same high-level structure as ISO 9001 and ISO 14001 (amongst other ISO Management System Standards). If you've already addressed Context of the Organization, leadership commitment, Document Control, Internal Audits, and Management Review for your quality or environmental system, you're not starting from zero.
The approach I typically recommend is to build on what exists rather than create a parallel system. Your Document Control procedures probably work fine - you just need to apply them to ISMS documentation. Your Management Review process already has a structure - you're adding information security elements as standing agenda items, not inventing a new meeting.
That said, there are areas where ISO 27001 requires things your Quality Management System never asked for. The Statement of Applicability is unique to 27001 - you need to review all 93 controls in Annex A and explicitly state whether each one applies to your organization, with justification for any exclusions. The Risk Assessment approach is more structured than what most Quality Systems require. And the controls themselves - covering everything from access management to cryptography to supplier security - go well beyond what ISO 9001 considers.
The manufacturer I worked with already had a corporate-level self-assessment tool that mapped to ISO 27001 controls, plus a Risk Assessment workbook from a certified sister company. We didn't throw those out. We reviewed what existed, identified what made sense for their specific scope and operations, and built the gaps. In some areas we used their existing approach. In others, we simplified - a 10-sheet Excel workbook with complex scoring across multiple tabs isn't practical for a team that needs to actually use and maintain the system.
The Risk Assessment Reality
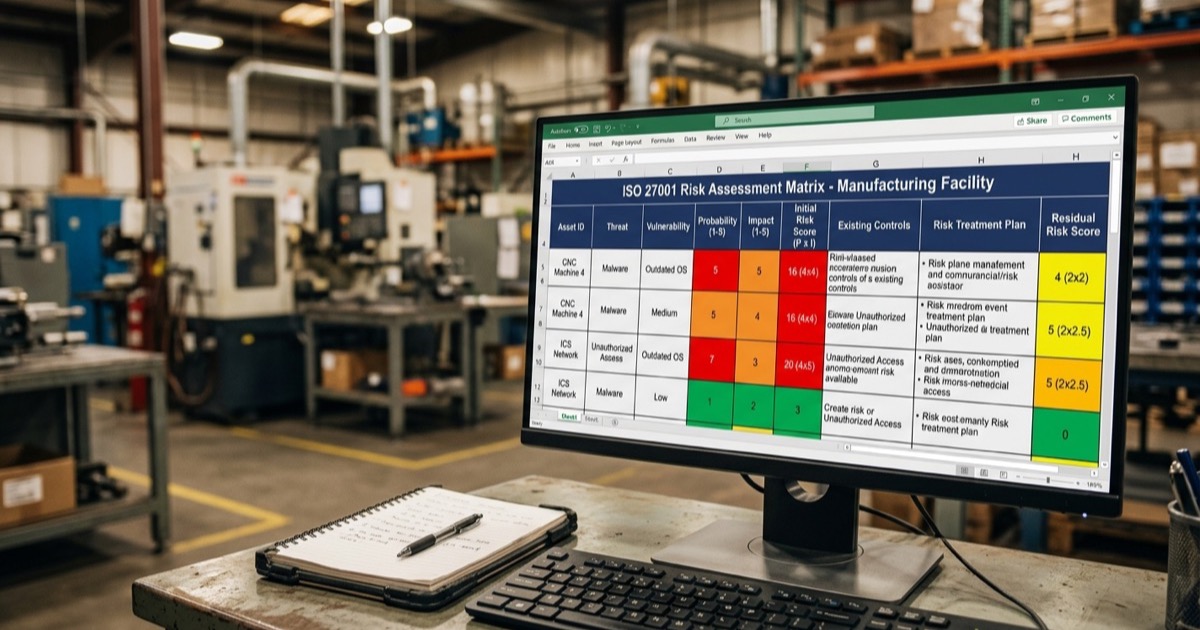
Risk Assessment is where I see the most overcomplicated approaches in manufacturing ISO 27001 implementations. Corporate IT departments love complex risk matrices with numerical scoring across multiple weighted factors - asset value times vulnerability rating times threat likelihood times impact score. The math looks impressive. The problem is that nobody actually uses it.
My bias is toward simpler approaches. A straightforward classification system - whether that's a 3x3 matrix or a low/medium/high rating across a few clear factors - is more likely to be understood, maintained, and actually inform decisions than a multi-tab scoring system that requires a manual to interpret. The standard doesn't prescribe how you assess risk. It requires that you have a method, that you apply it consistently, and that the results inform your treatment decisions.
For manufacturers, the Risk Assessment also needs to account for operational impacts that pure IT risk frameworks miss. A compromised email server is an inconvenience. A compromised ERP system that handles production scheduling, shipping, and Quality Records can halt operations across multiple plants. The risk scoring needs to reflect that reality.
What Auditors Actually Look For
Manufacturing companies sometimes worry that ISO 27001 auditors won't understand their environment. That concern isn't entirely unfounded - auditors who spend most of their time in office environments may need context about why your information security controls look different from a financial services firm.
But the fundamentals are the same. Auditors want to see that you understand your risks, that you've selected controls appropriate to those risks, that you've implemented what you said you would, and that you can demonstrate it with evidence. They're not expecting perfection - the standard has a Continual Improvement requirement precisely because no system starts perfect.
Where manufacturers get caught is the same place every organization gets caught: saying you do something that you don't actually do. If your change management procedure says all IT changes go through a formal approval process, but your IT team admits they only follow it a fraction of the time, that's a finding. Better to document a realistic process - maybe formal approval for high-risk changes and a lighter process for routine maintenance - than to write an aspirational procedure that nobody follows.
Practical Steps for Manufacturing Companies Considering ISO 27001
- Start with your existing Management System. If you're already certified to ISO 9001, ISO 14001 or similar, map out what you can leverage. Document Control, Management Review, Internal Audit processes, Corrective Action - these translate directly.
- Inventory your actual information assets. Don't just list IT equipment. Include production systems with network connectivity, custom applications, physical security infrastructure, and any controlled or classified information you handle.
- Review your customer contracts. Many manufacturers discover information security requirements buried in supply chain agreements that they haven't been formally addressing. Understanding these contractual obligations helps define your scope and justify the investment.
- Keep the Risk Assessment practical. You need a method that your team will actually use and maintain. If the person responsible for the ISMS can't explain how a risk score was calculated without consulting a reference guide, simplify it.
- Plan for integration, not isolation. Present your ISMS as part of an integrated Management System to your certification body. This can reduce audit time and cost, especially if the same registrar handles your other certifications.
- Budget four to six months for implementation. That's a realistic timeline for a manufacturing company with existing Management Systems to develop, implement, and prepare for certification - assuming steady effort and leadership support.
The Manufacturing Advantage
Here's something that might surprise you: manufacturers who already operate under ISO 9001 or ISO 14001 often have an easier time with ISO 27001 than companies implementing it as their first Management System standard. You already understand the audit process. Your leadership team already participates in Management Reviews. Your people already know what Documented Procedures and Objective Evidence mean. You're adding a lens - information security - to a framework you already operate within.
The manufacturing angle is also a genuine differentiator. Most ISO 27001 content online is written for technology companies (see our ISO 27001 articles for a manufacturing perspective). Most consultants specialize in IT environments. If you're a manufacturer pursuing certification, make sure you're working with someone who understands that your environment isn't a data center - it's a production facility where information security has to coexist with operational efficiency.
If you're working through an ISO 27001 implementation and want a second opinion on your approach, we offer a free initial consultation to help you figure out where you stand.
Trenton Steadman is the Lead ISO Consultant at Kaizen ISO Consulting. Since 2017 he has guided 200+ clients through ISO 9001, 14001, 45001, and 27001 certifications, with clients passing their certification audits on the first attempt. He also supports ISO 17025 and ISO 50001 engagements and holds AS9100 and IATF 16949 lead-auditor credentials. His approach is built around real operations rather than generic templates, so management systems work the day after certification, not just the day of.
Read Trenton's full profile