ISO 27001 Risk Assessment for Manufacturing
ISO 27001By Trenton Steadman
Quick Answer
What does ISO 27001 require for risk assessment?
ISO 27001 Clause 6.1.2 requires you to define risk acceptance criteria, identify information security risks, analyze likelihood and consequence, evaluate risks against your criteria, and produce consistent, valid, comparable results. The standard doesn't prescribe a methodology, scoring system, or matrix dimensions. A straightforward 3x3 matrix (low/medium/high for likelihood and consequence) satisfies the requirement; complex inherited corporate workbooks often fail because the maintenance burden outweighs the value, and an unmaintained risk assessment is worse than a simple one.
ISO 27001 Risk Assessment: When Complex Doesn't Mean Better
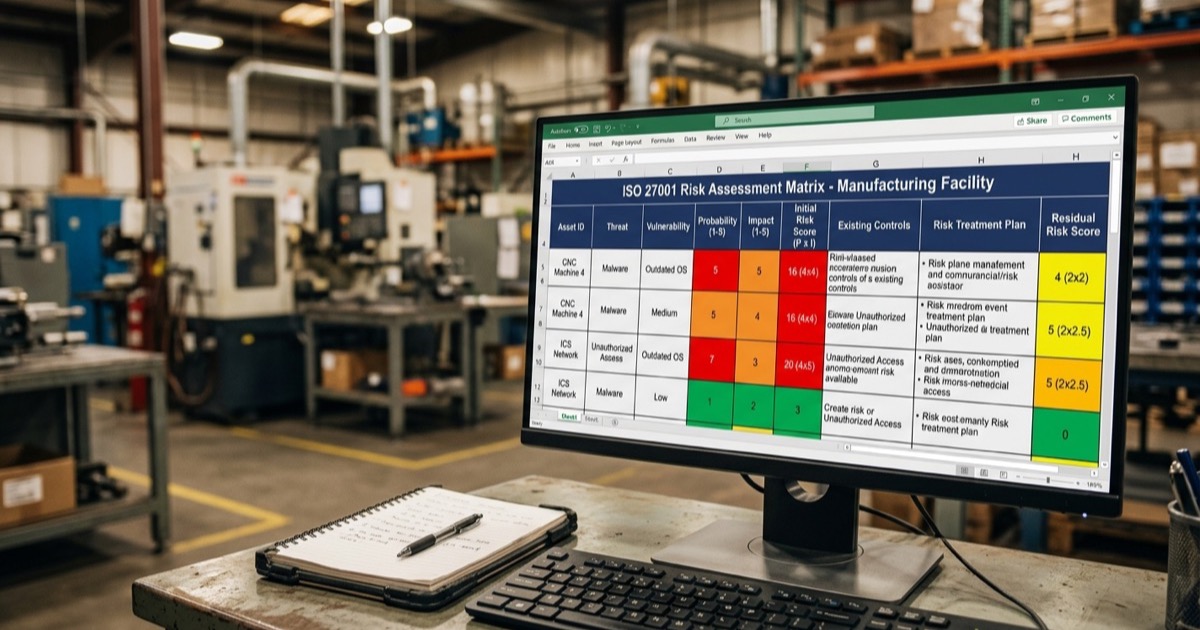
A manufacturing client recently showed me a Risk Assessment workbook they'd inherited from a sister company. It was a 10-sheet Excel file with asset values multiplied by vulnerability ratings, added to threat scores, cross-referenced across multiple tabs to produce a final risk classification. The math was sophisticated. The problem was that the IT Manager responsible for maintaining it couldn't easily explain how any individual risk score was calculated without tracing formulas across three separate worksheets.
That workbook met the requirements of ISO 27001. So does a straightforward 3x3 matrix with low, medium, and high ratings. The standard doesn't prescribe your methodology. It requires that you have one, that you apply it consistently, and that the results drive your treatment decisions. Everything beyond that is a choice - and the choice that matters most is whether your team will actually use the tool you build.
What ISO 27001 Actually Requires for Risk Assessment
Clause 6.1.2 of ISO 27001 lays out the Risk Assessment requirements. You need to establish and maintain a process that defines Risk Acceptance Criteria, identifies information security risks, analyzes those risks (assessing likelihood and consequence), evaluates risks against your acceptance criteria, and produces consistent, valid, comparable results. That's it. The standard says nothing about numerical scoring systems, weighted factors, or multi-variable matrices.
This distinction matters because I regularly see organizations - particularly those with corporate parent companies or sister divisions that are already certified - inheriting Risk Assessment approaches that are far more complex than necessary. The tools work. They meet the requirements. But they create a maintenance burden that's disproportionate to the value they provide, especially for manufacturing teams that are implementing ISO 27001 alongside existing quality and Environmental Management Systems.
The Problem with Inherited Corporate Risk Tools
Here's a scenario I see repeatedly in manufacturing: a company decides to pursue ISO 27001 certification. The IT manager reaches out to a certified sister or friendly company or corporate division for their Risk Assessment approach. What comes back is a workbook built for an organization with a dedicated information security team, different operational scope, and months of familiarity with a complex scoring methodology. Candidly, what you’re receiving was likely developed or also inherited based on assumed interpretations of ISO 27001 requirements and they very well may not make sense or work for you.
The workbook typically has separate sheets for asset classification, vulnerability assessment, threat identification, and risk calculation. Each sheet feeds into the next through formulas. Risk values are computed by combining asset values (rated 1-5) with vulnerability ratings (1-4) and threat likelihood scores (1-5), producing numbers that map to a classification legend on yet another sheet. Individual risk entries might reference policy documents by internal codes that don't exist in the receiving organization.
The IT Manager looks at this and thinks: "I don't have anything like this. This must be what's needed." But what's actually needed is much simpler - and what's needed is something that person will maintain twelve months from now when the initial implementation energy has worn off.
A Simplified Approach That Works
The approach I recommend for most manufacturing clients uses a 3x3 likelihood-and-consequence matrix. Here's what that looks like in practice.
Step 1: Define Your Criteria
Before identifying any risks, establish what low, medium, and high mean for your organization. This is context-specific - a "high consequence" event for a 50-person manufacturer is different from a multinational corporation. Keep the definitions grounded in business impact: production downtime, financial loss, regulatory exposure, customer impact.
For likelihood, think in terms of realistic timeframes. "High" might mean you'd expect this to occur within the next year given current controls. "Low" might mean it's theoretically possible but you have no evidence suggesting it's likely. The definitions don't need to be precise to the decimal point. They need to be understood consistently by everyone who uses the register.
Step 2: Identify and Describe Risks
For each risk, capture the scenario in plain language. "Unauthorized access to customer technical specifications through compromised credentials" tells you more than a risk ID code and a cryptic two-word description. Include what's affected - is this a confidentiality risk, an integrity risk, an availability risk, or some combination? The CIA triad isn't just a textbook concept. It helps you think clearly about what you're actually protecting and why.
For manufacturing environments, don't limit your thinking to traditional IT risks. Production systems going offline, calibration data being corrupted, ERP system downtime affecting shipping - these are information security risks even though they manifest on the production floor.
Step 3: Assess and Score
Rate likelihood and consequence as low, medium, or high. The combination gives you your risk level. A 3x3 matrix produces nine possible combinations, which is more than enough resolution for most manufacturing organizations. You don't need 25 risk levels from a 5x5 matrix when the difference between a "12" and a "13" on a numerical scale is essentially arbitrary.
The key discipline here is consistency. If you rate the likelihood of a ransomware attack as "medium," make sure a similar probability event elsewhere in the register also gets "medium." This is where having clear criteria definitions pays off.
Step 4: Document Current Controls
For every identified risk, note what you're already doing about it. Multi-factor authentication, encrypted storage for controlled data, access restrictions on production systems, backup procedures - these are existing controls that reduce risk from its raw state. This step is important because it gives your organization credit for the security practices you've already implemented and it shows the auditor that you understand your current posture.
Step 5: Assess Residual Risk
After accounting for current controls, reassess. If you identified a high-likelihood, high-consequence risk but you've already got strong controls in place, the residual risk might drop to medium or low. This is the risk level you're actually operating at, and it's what drives your treatment decision.
Treatment options are straightforward: treat the risk (implement additional controls), accept it (the residual level is within your tolerance), transfer it (insurance or outsourcing), or avoid it (eliminate the activity that creates the risk). For most manufacturing risks, you're choosing between treating and accepting. Document the decision either way - particularly for medium and high residual risks, where you'll want leadership sign-off on acceptance decisions.
Step 6: Plan Additional Actions
Where residual risk exceeds your acceptance criteria, identify what you'll do about it, who owns it, and when. These become your Risk Treatment plans. They don't all need to be completed before your certification audit - but they need to exist, have owners, and show progress.
What About Linking to Controls?
A common question I get: should the Risk Register cross-reference the 93 controls in Annex A? It's not an explicit requirement. The Statement of Applicability is where you address each control - whether it applies, why or why not, and the implementation status. Some organizations create explicit links between Risk Register entries and specific Annex A controls, and that can be valuable. But it also creates a maintenance burden.
My typical recommendation is to keep the Risk Register and the Statement of Applicability as separate but complementary documents. Start simple. If an auditor suggests linking them, you can always add a column. It's much easier to add structure than to strip away complexity from a system that's already overwhelming your team.
Making It Audit-Ready
Auditors will want to see a few specific things in your Risk Assessment approach, regardless of how simple or complex it is:
- Defined criteria. How did you determine what constitutes low, medium, and high? This should be documented somewhere - a tab in the workbook, a section in the ISMS manual, or a standalone document.
- Consistent application. Similar risks should have similar scores. If an auditor sees wildly different ratings for comparable scenarios, they'll question whether the criteria are being applied consistently.
- Risk ownership. Every risk should have someone accountable for it. In manufacturing, this often maps to functional roles - IT risks to the IT manager, physical security risks to facilities, production system risks to operations.
- Treatment decisions. For each risk, what's the decision? Treat, accept, transfer, avoid? If it's accepted, who approved that decision?
- Evidence of review. The Risk Register isn't a one-time document. You need to show that it's been reviewed and updated - at minimum during Management Review, but ideally whenever there's a significant change to your environment or a security incident.
A simple, well-maintained register with clear criteria, consistent scoring, and documented treatment decisions will satisfy an auditor far more effectively than a complex tool that the organization can't explain or hasn't updated since initial implementation.
Integration with Existing Management Systems
For manufacturers already running ISO 9001 or ISO 14001, there's good news: you've probably done something similar before. Environmental Aspects logs in ISO 14001 use a comparable approach - identify Environmental Aspects and associated impacts, assess significance using defined criteria, determine controls, and monitor. The concepts translate directly, even though the subject matter is different.
One Quality Manager I worked with immediately recognized the parallels between the information security Risk Register and their Environmental Aspects approach. Same structure, same logic, different lens. That's exactly the right way to think about it. If your team already understands how to assess and manage environmental risks using defined criteria and a significance determination, they can apply the same thinking to information security risks.
This isn't just a conceptual benefit - it has practical audit implications. When your Risk Assessment approach is consistent across Management Systems, you present a coherent picture of how your organization thinks about and manages risk. That builds auditor confidence far more effectively than having three different methodologies for three different standards.
Start Simple, Build as Needed
The best Risk Assessment tool is the one your team will actually maintain. Start with a clean 3x3 matrix, clear criteria, and plain-language risk descriptions. If you discover over time that you need more granularity - maybe you want to separate likelihood from frequency, or add a factor for detectability - you can always evolve the tool. It's much harder to simplify a complex system after people have invested time learning it than to add structure to a simple one.
The standard is flexible on methodology for a reason. Different organizations face different risks in different contexts. What matters is that your approach works for you - that the people responsible for the ISMS can explain it, maintain it, and use it to make informed decisions about where to focus your security resources.
If you're developing an ISO 27001 Risk Assessment and want a second perspective on your approach, we offer a free initial consultation to review where you stand and where to focus your efforts.
Trenton Steadman is the Lead ISO Consultant at Kaizen ISO Consulting. Since 2017 he has guided 200+ clients through ISO 9001, 14001, 45001, and 27001 certifications, with clients passing their certification audits on the first attempt. He also supports ISO 17025 and ISO 50001 engagements and holds AS9100 and IATF 16949 lead-auditor credentials. His approach is built around real operations rather than generic templates, so management systems work the day after certification, not just the day of.
Read Trenton's full profile

